Check out our White Paper Series!
A complete library of helpful advice and survival guides for every aspect of system monitoring and control.
1-800-693-0351
Have a specific question? Ask our team of expert engineers and get a specific answer!
Sign up for the next DPS Factory Training!

Whether you're new to our equipment or you've used it for years, DPS factory training is the best way to get more from your monitoring.
Reserve Your Seat TodayMany industries deploy Supervisory Control and Data Acquisition (SCADA) systems in order to leverage their network's level of reliability, performance, and security. However, these deployments often fail due to various reasons, leaving you with an unprotected network and a mess to clean up.
As an experienced SCADA manufacturer, many clients come to us after their initial deployment with another company has failed. Time and time again we find the same list of common mistakes that are serious enough to affect the success of your SCADA investment.
Here's a list of things you should avoid in order to improve your chances of making your SCADA system pay off for your company.
A common issue that prevents SCADA project success is not knowing what you can expect from this technology. It's important to understand how the system works, its characteristics, and how you can use it to minimize your pain points and achieve your goals.
Simply assuming that your SCADA system will perform in a certain way, might be setting yourself up for failure. So, before making the decision to invest in a SCADA application, make sure to do thorough research about this technology.
Usually, SCADA systems have a master/slave architecture.
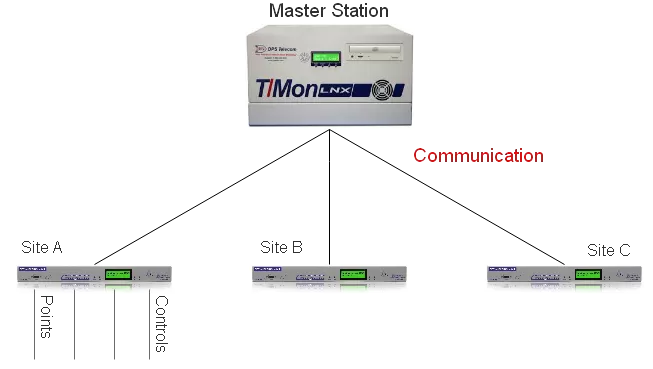
The slaves are remote terminal units (RTUs) configured to collect local data and send it to the master. They also perform control functions directed by the master. The master is a central computer programmed to receive and process information received from the RTUs. They provide you with an interface to your system, send you notifications about events, and transmit control instructions to the slave devices.

The master station and the slaves communicate through a protocol. The protocol is the determined language used by the devices within a network.
Communication protocols can be designed around a polling method or around a push method.
The polling method makes it so the communication starts at the master station. The master will ask for a change of status update from each slave device, from the first to the last one. When it reaches the last device, it will start again from the beginning - the polling loop. The problem with this method is those slave devices have to wait their turn to be polling in order to communicate a problem.
With a push method, each remote field device is programmed to intelligently transmit its data to the master device. The transmission can take place at set intervals (every five seconds for example) or when certain conditions happen, such as a piece of equipment reaching a certain temperature or the voltage in an electric line reaching a critical point.
The industry's best practice is adopting both methods if possible. Failing to adopt the push method as well can put your project in jeopardy.
For example, we have a client that, over the course of five years, tried different SCADA systems from different vendors. As a natural gas field services provider, they need to monitor their compressors along with its pipelines, using satellite communication transport. Every time there was a glitch in the communication, the entire poll started over. This rendered their SCADA system unreliable and they had to deal with expensive satellite service fees. It was not until they reached out to us and we proposed an SNMP solution with traps messages that this issue was resolved.
Especially, if you can access your SCADA system over the internet, it's important to keep in mind its security and continuity. The internet exposes your system to a variety of security and reliability threats that can be a major headache if not handled correctly.
Internet-based systems are excellent targets for viruses, malware and hackers.
Your SCADA system has sensitive information about your network and can control your remote equipment. So, if an attacker manages to break into your system they can corrupt your information, trigger false alarms, suppress actual alarms, or even take control of your remote devices. Each of these security breaches can cause devastating impacts to your network, operations, and end-users.
Your SCADA investment will be useless unless you don't take proper action to secure your system by continuously monitoring any activities, encrypting your information, and performing regular back-ups of data. It's critical that your vendor can provide you with a secure SCADA solution with these capabilities.
Most SCADA vendors are good at providing the off-the-shelf, generic data acquisition, and control capabilities. However, no network is exactly the same. Different organizations will require data to be collected, processed, and displayed in very specific ways depending on what their bottom line is. For example, the type and format of information used for alarm notifications and trend reports in a gas plant will be different than for an electric substation network.
Don't make the mistake to invest in an off-the-shelf SCADA system when you have very specific requirements. Work with a manufacturer that is experienced in customizing and configuring SCADA solutions in order to provide perfect-fit systems.
Also, make sure you are not locking yourself into proprietary protocols.
Imagine that you are with a utility company that decided to invest in a SCADA system to monitor aging transformers to optimize their throughput and reliability. Instead of using devices support open-standard communication protocols, you chose remote monitoring units running on a proprietary protocol.
As a result, you were unable to integrate your legacy equipment into your SCADA application. And if you need any additional monitoring device, you'll have to purchase it from the same vendor every time - otherwise, you won't be able to smoothly integrate this new equipment to your system.
You'll be in a better position if you choose a vendor that is able to provide you with an open and scalable SCADA system. This way, you'll get all the benefits of open interoperability across your network. You'll be able to slowly replace legacy devices, and change your monitoring, control functions, alarming features, and trend analysis as your network grows.
Some SCADA manufacturers want to impress customers by stuffing bells and whistles in their software applications, overbuilding the screens that you'll be interacting with. The problem is, they often forget how a user-friendly interface should be.
The result is a confusing screen with a mixture of lists, unclear schematics, and overall obscure information. A web interface like that won't help you get real-time visibility over your network.
Also, most manufacturers think that the more data you have the better analysis you can make. However, they often forget to implement nuisance alarm filtering. This overload both your team and your system with notifications about events that are not important.
When you and your team have to dig through the screens and the overload of unimportant notifications, it makes it hard to get them on board with the application. This ultimately means that you'll be spending more time and money with training and tech support.
So, instead of being overwhelmed with every piece of available data and confusing interfaces, look for vendors that can offer a simple and user-friendly interface. These interfaces will display important data in a map, using colors to highlight critical alarm conditions.
Another reason SCADA projects lack efficiency is that decision-makers base the purchase only on price. This is never a good idea, especially because this system is supposed to protect your bottom line.
Vendors that offer very cheap systems might be small businesses trying to get established in the market and may not even be able to support themselves long enough until you finish your deployment. They might go out of business and leave you with no after-sale support and no possibility for system upgrades.
Companies that provide cheap SCADA systems are probably outsourcing most part of their work from overseas. This leads to quality, language, and cultural problems. On the other hand, make sure that vendors offering expensive systems are not young companies trying to charge as much as they can in order to pay for their initial investments and to stay in business.
Instead of looking only at the price tag, it's critical that you make sure your vendor is an experienced manufacturer with many years in the market. Experienced vendors have helped hundreds of known companies and can provide you with testimonials and referrals. These are the companies that can deliver cost-effective SCADA systems.
As I've said previously, depending on the vendor, you might see yourself left with no support whatsoever after your equipment purchase.
Buying tech support after you already deployed your SCADA system can be very expensive because you are already fully committed to this particular vendor's solution. This means that they won't have much reason to negotiate their prices, after all, you are already bought your system so you need their support.
The time to make sure you'll have quality tech support is before your project starts. Before signing anything, be sure to negotiate after-sale services, such as tech support and training. Your vendor should be able to provide good and reliable after-sale services.
SCADA technology is critical to many organizations because it can reduce expensive repair and maintenance visits to remote sites, it can enhance the reliability and efficiency of the network being monitored, and it can allow teams to respond in a timely manner to failure of critical equipment.
If you are armed with the knowledge of the most common SCADA pitfalls, you'll be well-positioned to deploy a successful project and quickly begin reaping the benefits of an efficient system. Also, by counting on a competent vendor, you can bring your plans of an efficient SCADA to life.
And we can help you with that. About 80% of everything we sell was custom-made for our clients. We design our software solutions and build industry-grade hardware in-house, so it's easy for us to provide reliable perfect-fit solutions. Call us today and start treating us your personal engineering department.

Morgana Siggins
Morgana Siggins is a marketing writer, content creator, and documentation specialist at DPS Telecom. She has created over 200 blog articles and videos sharing her years of experience in the remote monitoring industry.