Check out our White Paper Series!
A complete library of helpful advice and survival guides for every aspect of system monitoring and control.
1-800-693-0351
Have a specific question? Ask our team of expert engineers and get a specific answer!
Sign up for the next DPS Factory Training!

Whether you're new to our equipment or you've used it for years, DPS factory training is the best way to get more from your monitoring.
Reserve Your Seat TodayHaving efficient network monitoring and traffic management systems is critical in order to ensure enhanced network performance. The SNMP protocol and NetFlow offer different ways to keep an eye on your network traffic.
If you are involved in the networking world, you might be wondering - between these two protocols, which is better?
As network monitoring solutions experts, we can provide you important insights into what SNMP and NetFlow are and their main differences. So let's get started.
Simple Network Management Protocol (SNMP) is a common standardized application layer communication protocol. Mostly used for network monitoring, it is capable of monitoring and gathering data about a large number of network devices.
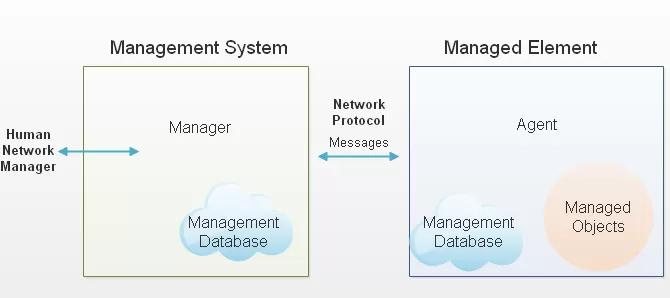
The SNMP Management Information Base (MIB) is a file loaded in managed devices and the master station. This file contains a set of pre-defined object identifiers (OIDs) which ensures that the managed devices and the master station can communicate together. That's how the SNMP protocol can monitor almost anything in your network, such as room temperature or incoming and outgoing traffic.
In a nutshell, SNMP is an important technology for measuring and understanding your remote network.
In contrast to SNMP, NetFlow was developed with network traffic monitoring in mind. In fact, Flow technologies, including NetFlow, sFlow, jFlow, and others, are used to describe traffic on a network.
These technologies export data that describes the exchange of information happening across the specific network device. This includes port, IP source, destination, and port numbers.
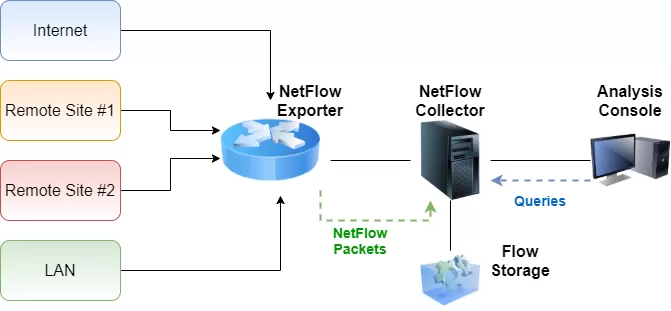
In other words, NetFlow enabled devices examine each packet and the first unique packet creates a flow as an entry in NetFlow cache. The other packets that match the same parameters are aggregated to this flow and the bytes counter for the flow increases. If any of the parameters don't match, a new flow is created in the cache.
Flow records are then exported from exporters to one or more NetFlow collectors. However, if a NetFlow enabled equipment doesn't receive IP traffic, flows are not created in the cache and are not exported to a collector. This is process is similar to SNMP traps that are sent to the master station when an important change of status is detected.
SNMP is used by operationally focused network technician and network managers that want to understand the key indicators that show problems in the health and operation of the network. This includes the devices themselves and the links between them. The SNMP data is also used by network technicians to troubleshoot issues and to perform proactive hardware maintenance.
NetFlow, on the other hand, is used by network technicians to understand traffic, why congestion or heavy usage is happening, what is causing traffic changes and how these changes can be eliminated. These analytics are used to make decisions on how traffic is being sent or received to other internet-connected coworkers through traffic engineering and optimization.
Basically, SNMP gives you the answer to "what" is happening on your network, while NetFlow answer the "where" and "who".
One of the main differences between SNMP and NetFlow is when network technicians decide to use these protocols.
SNMP can be used by a master station to proactively poll (ask) network agents to collect information about remote devices. This process is used during discovery to figure out what kind of device it is and is used to gather data about the device, such as the vendor, when it was last configured, and what kind of hardware the device is.
Aside from that, you can also collect numerical data. This is useful to understand the status and usage of any particular subsystem on the device. Each time the agent is polled and data is sent back in response, your master station collects the information to build a trend analysis report.
The challenge with the SNMP protocol is that you can define the polling interval as long or as short as you want (or as required). Most technicians set their master stations to poll at 1-5 minutes intervals, but as you might already know, during this 5-minute interval many alerts and change of status can be missed.
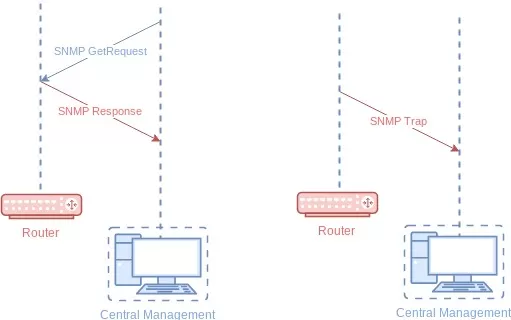
This challenge is addressed by either increasing the frequency of the polling or by deploying an SNMP system that supports trap messages.
Flow technologies are important data sources when measuring what, where, and how actual traffic is passed through a device.
While this can be applied to a single device, flow becomes much more interesting when you integrate and combine traffic data with additional sources to be able to measure traffic moving between devices. Doing this enables you to understand the end-to-end traffic flow and conversation. Which includes adding in high-value data, such as threat feed and threat modeling, routing, topology, and other important networking information to model answers to hard questions.
NetFlow can also be used to understand the consumption of bandwidth in a more detailed manner. For instance, looking per IP, per network and even into virtual constructs, such as MPLS, VPNs, and other virtual router devices allows for a much deeper understanding of the traffic.
Another important point to keep in mind is that, with sampling, you can collect a very small set of data to describe high volumes of traffic. This allows flow technologies to scale much better than packet-capture solutions while also giving you vital insights into the traffic and traffic patterns on the network.
While not as accurate than describing and inspecting all of the packets in terms of application depth and performance data, flow can easily monitor traffic sampled or not sampled with much less required hardware or potential security issues.
As we've talked about previously, SNMP uses polling and traps.
Polling is when a master station periodically sends SNMP Get Requests to an SNMP agent, requesting it to send OID values. The agent then replies to the master station with SNMP Get Responses, carrying the OIDs with their measured values.
SNMP traps are sent by agents to the master station when an important event occurs. For example, when temperature value goes beyond the set thresholds and an alarm happens.
Comparable to SNMP, NetFlow works just like the trap method. It sends flow records from a cache to a flow collector. A flow is exported from the exporter (a NetFlow enabled switch or a router) based on inactive flow timer when no other packets are received for a particular flow within an inactive timer (this is 15 seconds by default).
A flow may also be export when an active timer is reached (this is 30 minutes by default) and another packet of the same flow enters the interface with an enabled flow export. In both cases, flow records are pushed out of the exporter with no request necessary from the collector.
SNMP works by collecting information about bandwidth usage of network devices on a port-by-port basis. So, if you need to gain network visibility while also knowing how much bandwidth is being used, this protocol is perfect for that.
As I've said before, SNMP gives you an answer as to "what" is going on at your network, but it lacks the information such as "who" (source hosts) and "where" (destination hosts). These SNMP limitations block technicians from pinpointing the root cause of problems that affect network performance such as misconfiguration and excessive bandwidth utilization.
Different from SNMP, NetFlow is good at giving you all this information in the form of NetFlow records. This allows you to characterize traffic based on parameters such as source IP address, the destination IP, application protocol, and number of packets.
SNMP packets are continuously sent across the network in real-time (every second for example) as responses to master station queries.
On the other hand, the exporting of NetFlow records depends on active/inactive timers. This means it can take up to 30 minutes to export a flow when NetFlow is being used.
SNMP is clearly better in terms of traffic visibility than NetFlow. If that's an issue for you but you still need to use Flow technologies, you could use sFlow instead of NetFlow. sflow doesn't cache data, its packets are instead sent in real-time to a collector where they are analyzed.
SNMP is the oldest network management protocol used today. It was defined by the RFC 1157 in the 1990s but the design of its first version (SNMPv1) was already developed in the 1980s. So, since then, this protocol has been widely adopted by multiple network vendors. Even the newer generation of network devices that support NetFlow still support SNMP.
NetFlow is a much younger protocol and it's not as common as SNMP.
The SNMP protocol usually uses the UDP port for the transport of communication. SNMP agents use UDP 161 and the master station uses UDP 162.
NetFlow also uses the UDP port, but the most modern version of NetFlow can also use the Stream Control Transmission Protocol (SCTP) when a reliable transport is needed.
NetFlow and SNMP provide you with two different approaches to network monitoring.
If you need interoperability between devices from different vendors, real-time monitoring, and low resource consumption (especially true for SNMPv1 and SNMPv2c with no authentication nor encryption features), then you should use SNMP if possible. Also, SNMP is critical to remote monitoring systems in order to detect and prevent network failures - including hardware fault management. All these capabilities make SNMP one of the most commonly used communication protocols today.
However, this protocol doesn't tell you who and with that is consuming your bandwidth, for that, you need NetFlow.
This means that the best practice for network monitoring is to combine both methods. SNMP will help you with fault management and network performance monitoring while NetFlow will provide you an accuracy of the network traffic parameters. You need both sets of data to make informed decisions and to optimize your entire network.
If you need more information about how to use the SNMP protocol, a good way to start is reading our SNMP Tutorial White Paper. With concrete real-world applications, you'll learn how to use SNMP for network alarm management.
Download your PDF copy or contact us today.

Morgana Siggins
Morgana Siggins is a marketing writer, content creator, and documentation specialist at DPS Telecom. She has created over 200 blog articles and videos sharing her years of experience in the remote monitoring industry.