Check out our White Paper Series!
A complete library of helpful advice and survival guides for every aspect of system monitoring and control.
1-800-693-0351
Have a specific question? Ask our team of expert engineers and get a specific answer!
Sign up for the next DPS Factory Training!

Whether you're new to our equipment or you've used it for years, DPS factory training is the best way to get more from your monitoring.
Reserve Your Seat TodayAs you familiarize yourself with new protocols and devices, trying to diagnose issues or network connections can be a bit confusing at the device level. In response to many tech support requests, we decided to build this free network utility application to you (and our own engineers) troubleshoot the most common issues our clients face, as well as give you some useful network statistics.
Typically, network tools try to be way too smart and end up losing a lot of functionality. Instead, we built this tool to provide you with as much control as possible when troubleshooting, so you can ensure your devices work correctly.
Each tab listens for a specific protocol on its own port. Any available port can be used but some protocols have a standard value.
Ping/Traceroute uses ICMP and does not require you to set a port. If a port is in use already, a random port will be used instead. Setting the port to 0 will always choose a random port.
The message builder layout will change depending on the protocol type selected. The interval (in milliseconds) and repetition fields allow for repeatedly sending the same message at a regular interval. Repeated messages can be stopped by clicking the X next to the target IP in the bottom left corner of the application.
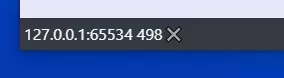
Canceling a repeated message.
You can also save a message to send later.
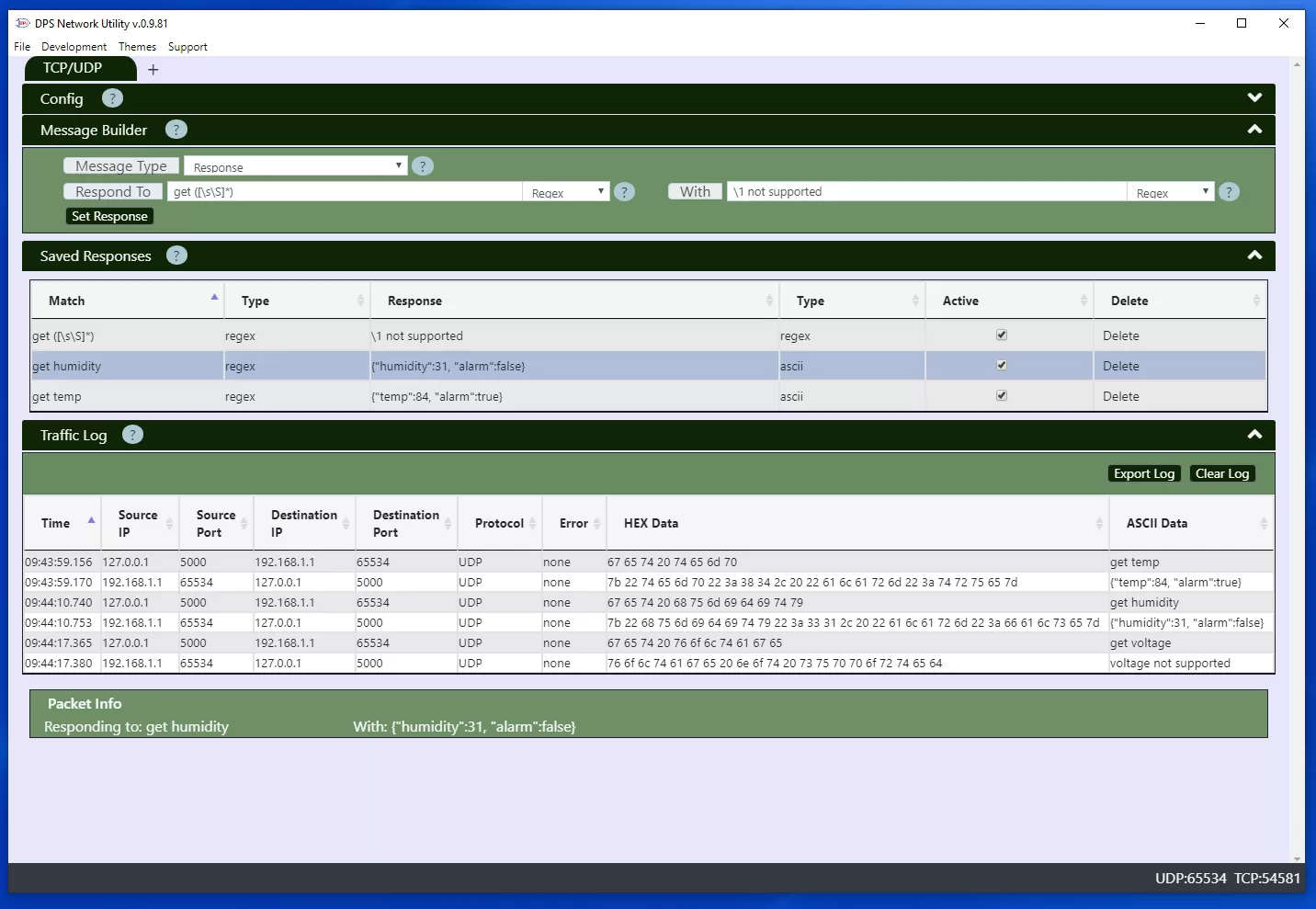
Automatic replies can be set up for incoming UDP/TCP packets and SNMP requests. UDP/TCP packets can be matched directly from their contents or by a regular expression. SNMP responses are matched by the request OID or optionally a previous OID value for get-next requests.
All traffic logs can be exported to a comma or space delimited log file. The default save location is in the logs folder but can be changed when saving.
Similar to a tool like Packet Sender, the app lets you test sending TCP and UDP packets. The content of the message can be entered as an ASCII string or space separated hex values. If the protocol is TCP, the connection will be closed after sending a message unless "Keep TCP connection" is checked. With it checked, you'll be able to continue sending messages over the same connection.
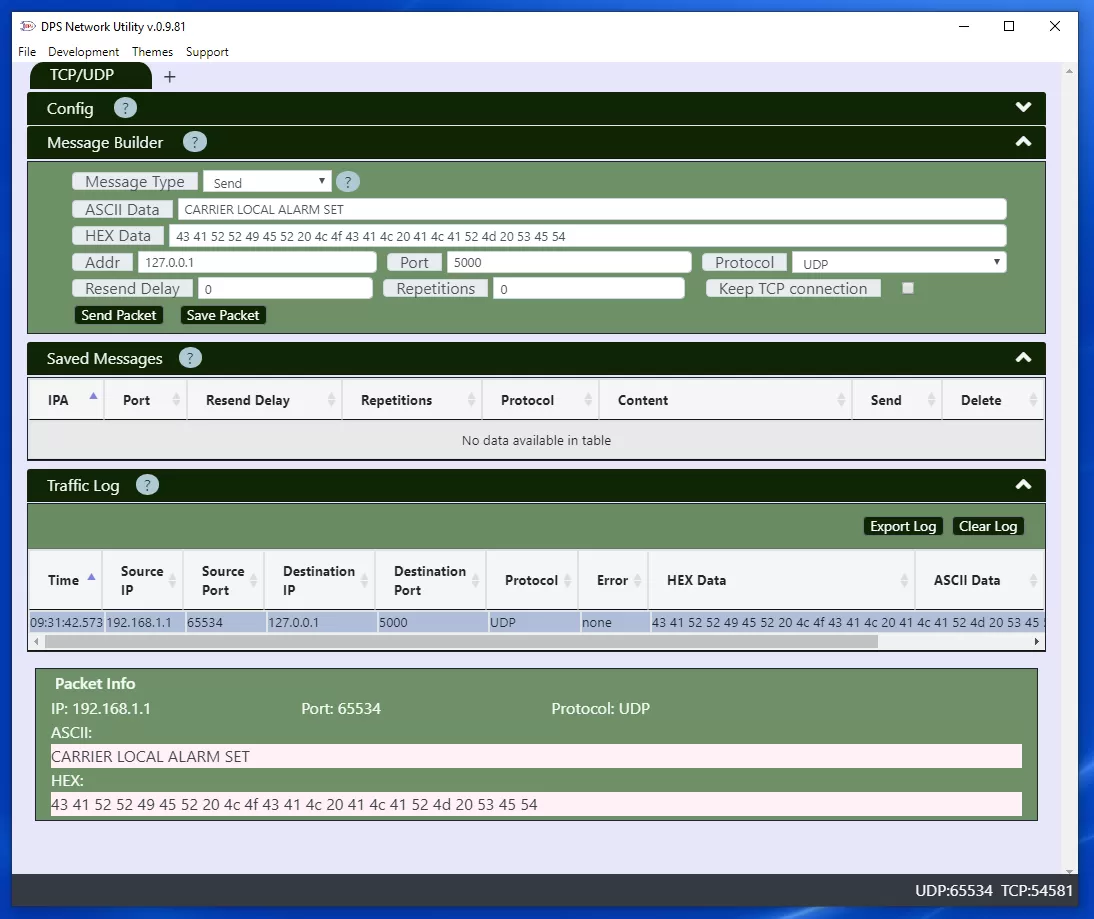
Sending a message over UDP.
Active responses are matched against incoming packets. If there are multiple responses set up, the first one that matches will be used. Packets can be matched based on:
ASCII and hex matches are a simple case insensitive comparison between the raw TCP/UDP data and the match string. Regex comparisons will be run against the ASCII content with the global and case insensitive flags on. Capture groups in the match string can be used in the response if the response type is regex as well.
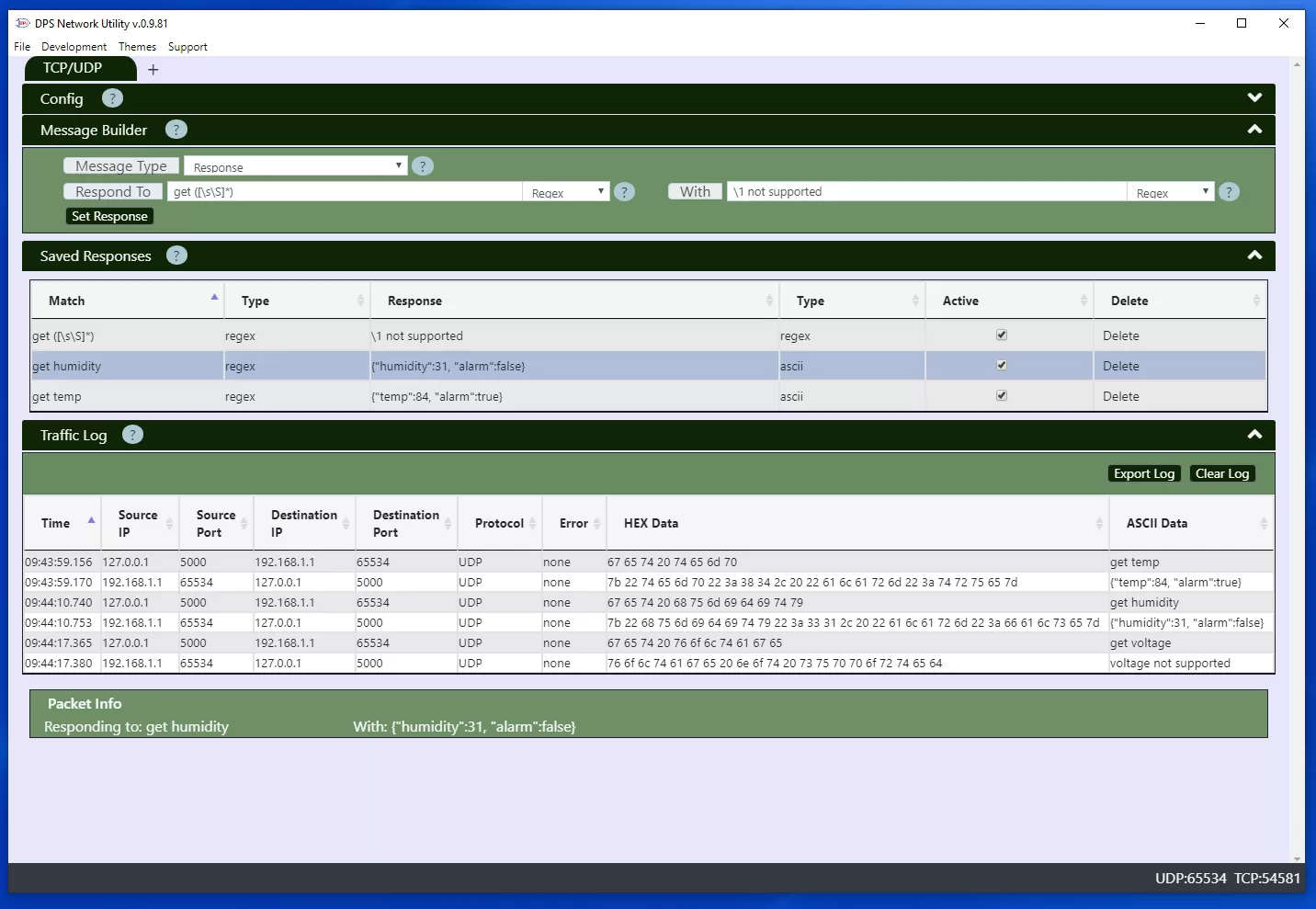
Setting up a TCP or UDP response.
SNMP troubleshooting with the Network Utility App can save you a ton of time versus trying to use your RTU to test SNMP requests. Using this tool, you can quickly simulate SNMP messages as a manager or agent. Simply fill out the appropriate fields to test your desired functionality.
Keep in mind, the value and data type must be specified for SET requests.
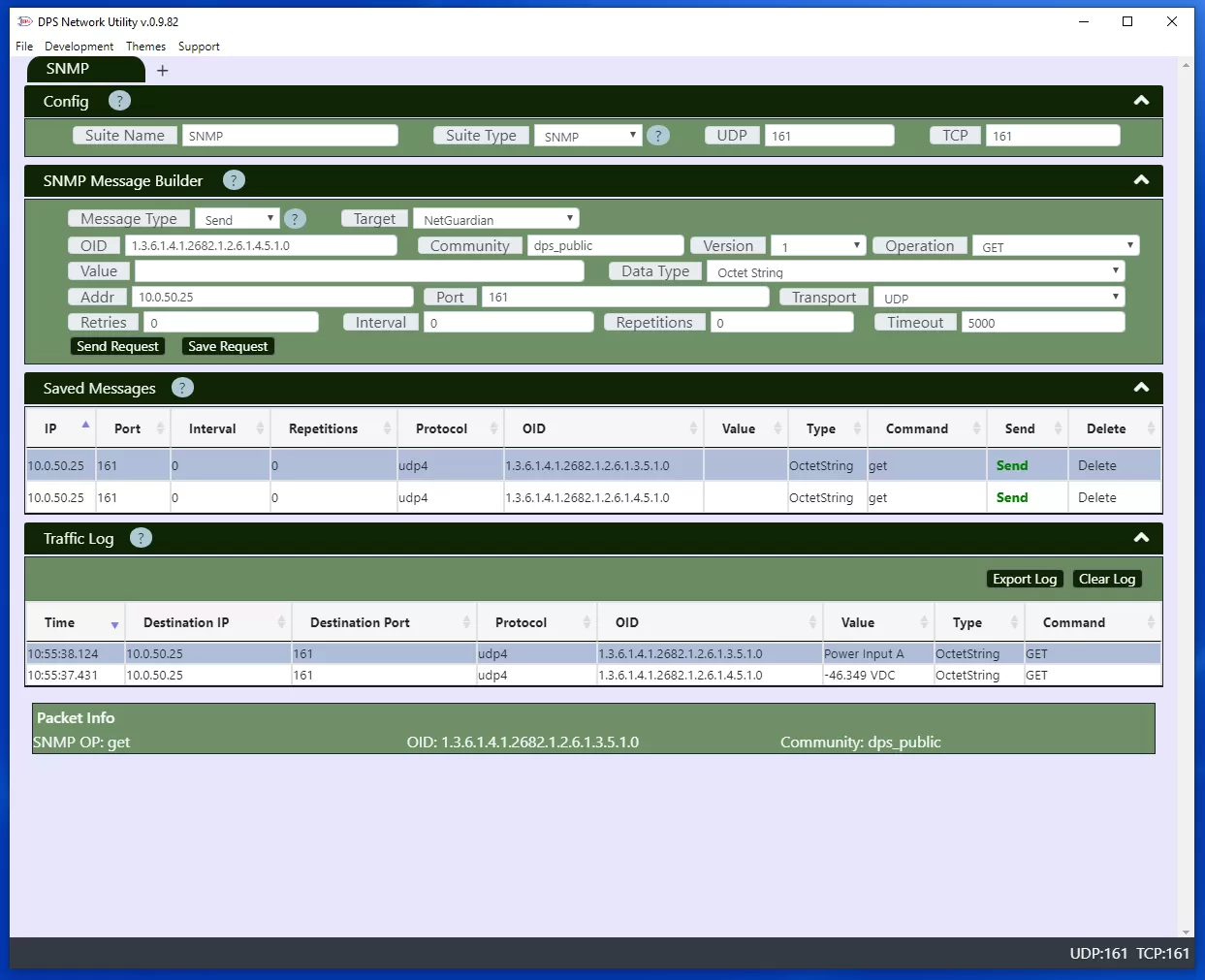
Sending a SNMP request.
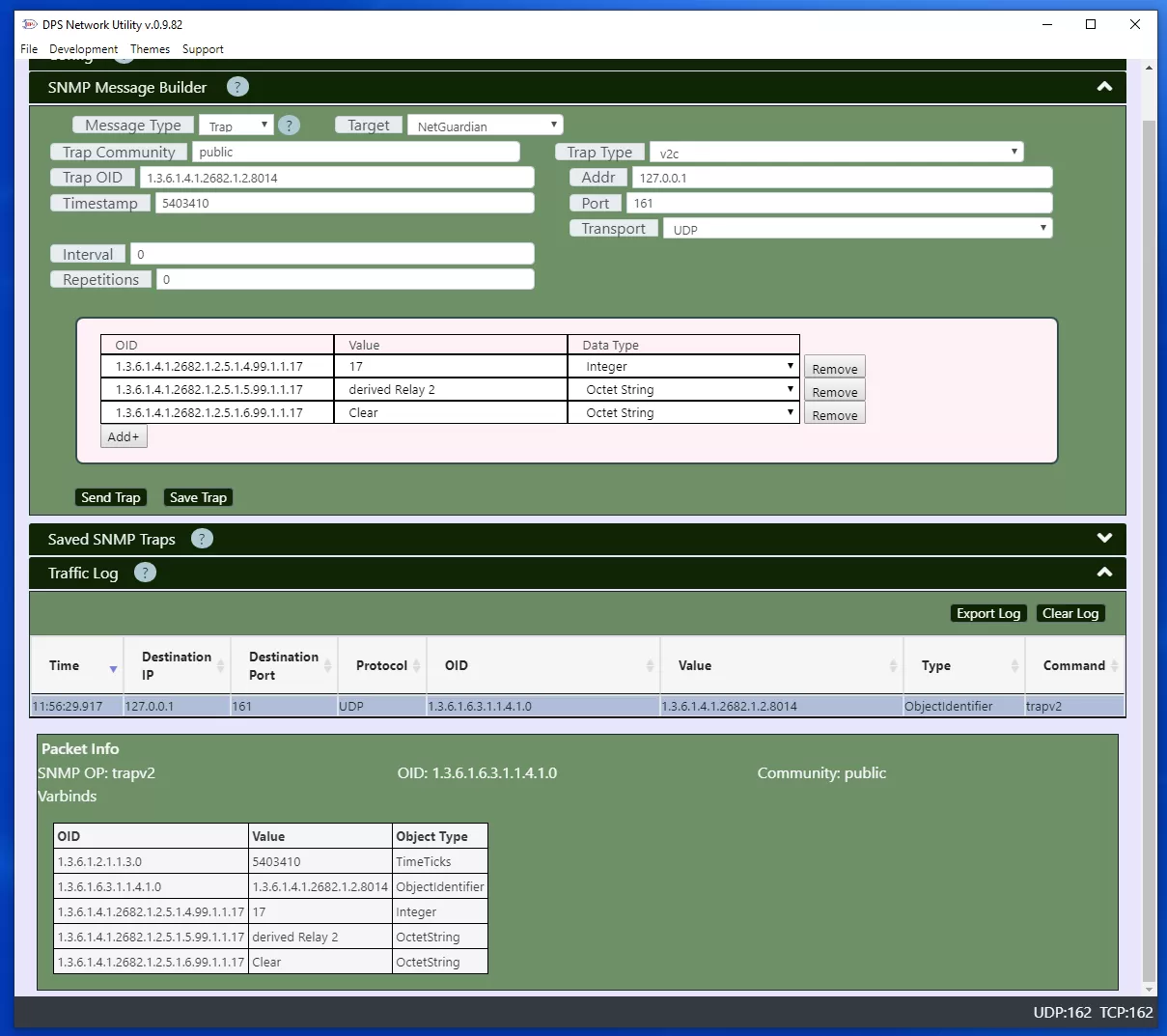
Sending a Trap.
A SNMP response will be sent when the response OID matches an incoming get or set request. If Previous OID is set then the response will also be sent if a get-next request for the previous OID is received.
DCP is the protocol used by DPS' T/Mon Master Station to poll a DPS NetGuardian. It is not a very popular protocol, but it is a very lightweight protocol which allows rapid polling of RTUs in the field, while consuming a very low amount of bandwidth. DCP troubleshooting can be tough if you've never experienced it, especially because there are not many tools or examples online that explain it. With DPS Network Utility, you will be able to simulate DCP polling from a T/Mon to a NetGuardian.
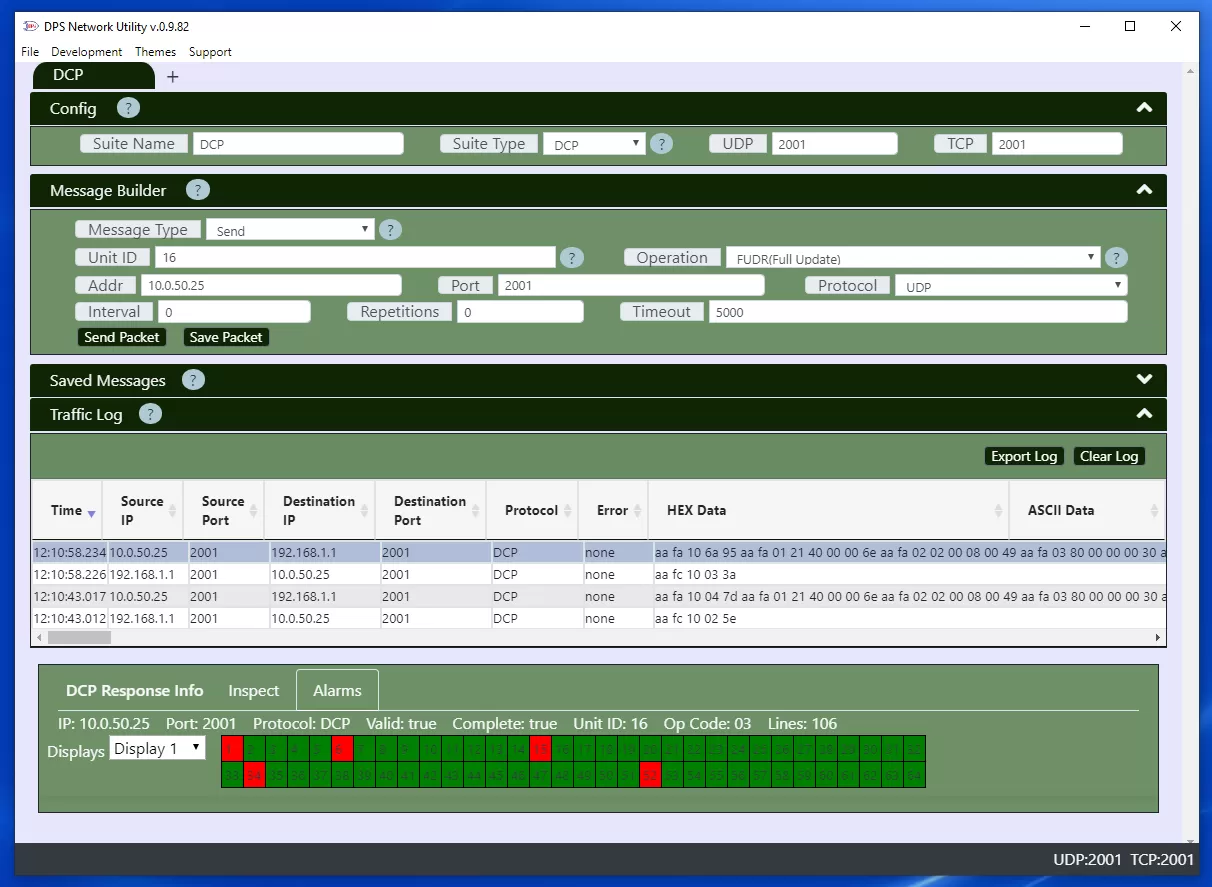
DCP is alarm collection and control protocol used on DPS devices.
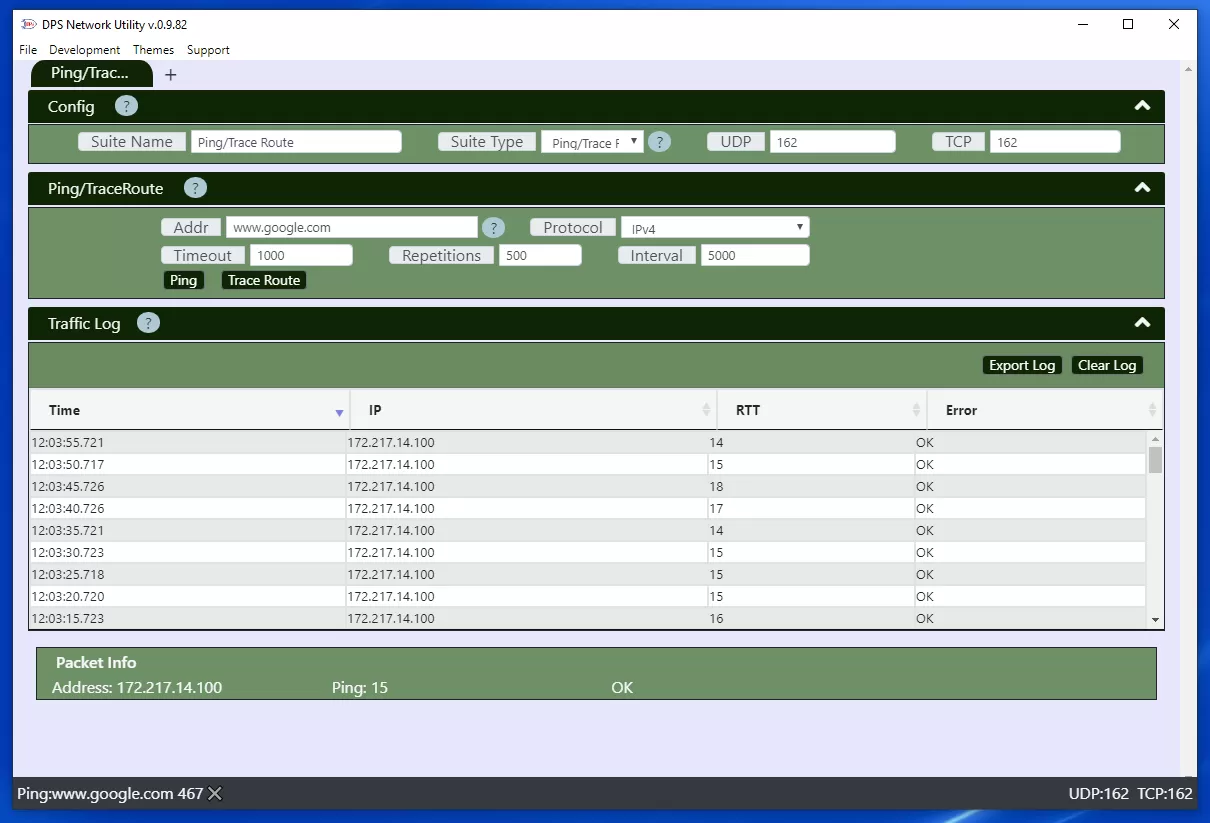
Pinging an address.
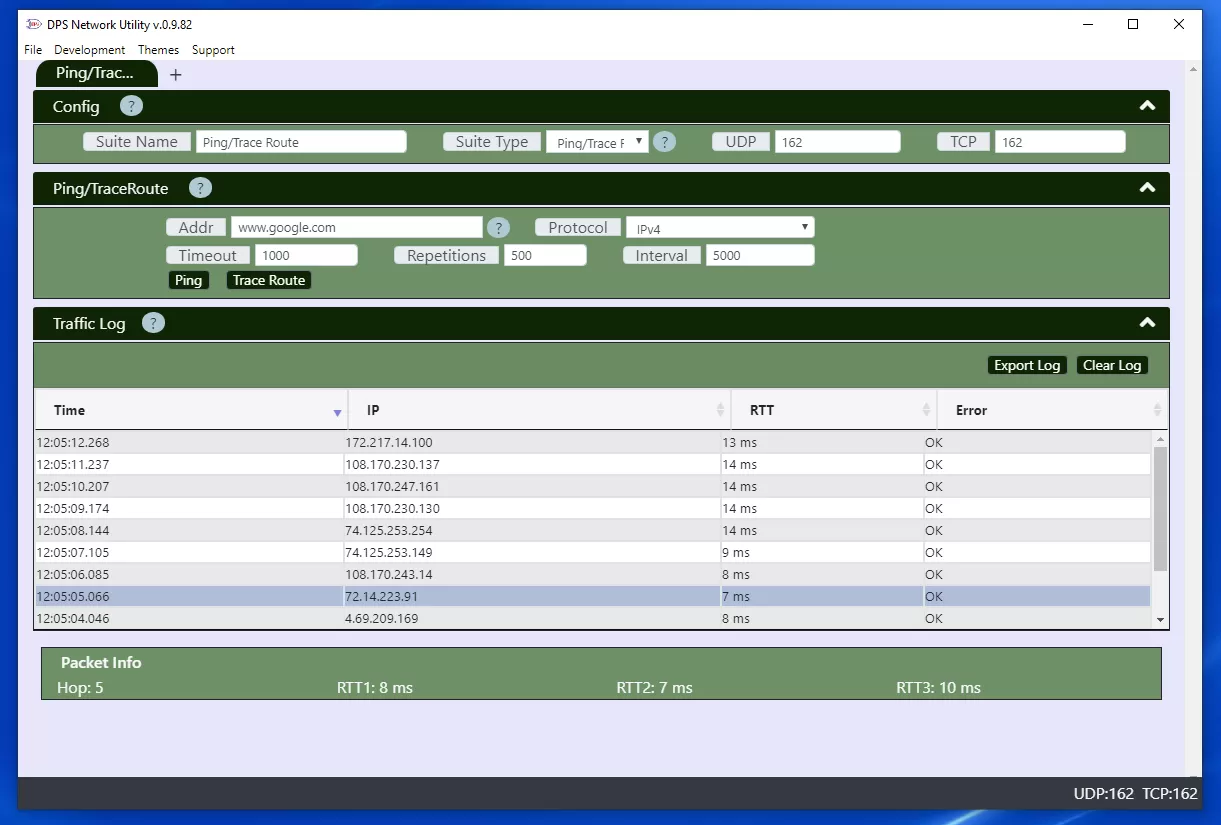
Tracing the route to an address.